Bitcoin users often focus on wallets and private keys, yet most real losses happen elsewhere. Exchanges and mobile apps are where daily activity happens. That also makes them prime targets. Attackers do not need to break the blockchain. They only need to exploit small mistakes made during logins, transfers, or app usage. A single careless click or weak password can open the door to serious loss.
Many users feel safe because they trust the platform they are using. That trust can be misplaced if basic precautions are ignored. Security is not only about technology. It is about behavior. The way you connect, verify, and interact with services shapes your risk level. This guide focuses on practical habits that reduce exposure without making your workflow complicated.
- Secure your login with strong passwords and layered protection
- Avoid logging in through public or unknown networks
- Verify apps and exchanges before trusting them with funds
- Stay alert to phishing attempts and fake notifications
- Use device level protections to prevent silent compromises
Why Exchanges and Apps Are the Weakest Point
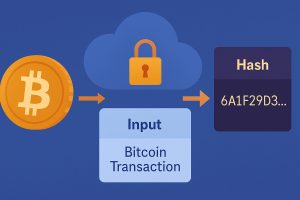
Bitcoin itself is designed to be secure. Transactions are verified across a distributed network. That part rarely fails. What does fail is the environment around it. Exchanges store funds in centralized systems. Apps run on personal devices that may not be hardened. These layers introduce vulnerabilities that attackers can exploit.
Users often reuse passwords across platforms. They may log in from shared devices or open WiFi networks. They may also install apps without checking their origin. Each of these actions increases the attack surface. Once an attacker gains access, funds can be moved quickly. Recovery is difficult and often impossible.
Understanding this shift in risk is important. The threat is not the Bitcoin protocol. It is the way users interact with services built around it. That is where most attacks happen.
Strengthening Your Login Defense
The first layer of protection starts with how you access your accounts. A password alone is no longer enough. Attackers use credential stuffing, brute force attempts, and phishing techniques to capture login details. Adding a second layer significantly reduces risk.
Using two factor authentication ensures that even if your password is exposed, access is still blocked without the second verification step. This simple measure stops many automated attacks and protects against reused credentials.
Beyond that, password hygiene matters. Avoid simple combinations. Avoid using the same password across multiple platforms. A password manager can help generate and store strong credentials. It also removes the need to remember complex strings.
Recognizing Fake Platforms Before It Is Too Late
Not every exchange or app is legitimate. Some are built to look convincing. They mimic branding, interface design, and even customer support responses. The goal is simple, gain your trust and capture your login or funds.
Many users only realize the problem after they attempt a withdrawal. By then, it is often too late. Taking time to verify platforms before using them can prevent this situation. Checking domain names, reading independent reviews, and avoiding unsolicited recommendations are key steps.
Learning how to spot warning signs becomes easier with practice. Suspicious URLs, rushed onboarding processes, and unrealistic promises are all indicators. For deeper insight into identifying risky services, reviewing patterns in fake bitcoin exchanges can sharpen your judgment.
Mobile Apps Are Convenient but Risky
Mobile apps make Bitcoin accessible at any time. That convenience comes with tradeoffs. Phones are exposed to more threats than desktop systems. They connect to different networks. They install multiple apps. They are also easier to lose or compromise physically.
Improving your mobile security reduces the chance of silent attacks. This includes keeping your operating system updated, installing apps only from official stores, and avoiding unnecessary permissions. A malicious app does not need to target Bitcoin directly. It can monitor inputs, capture data, or redirect traffic.
Even small actions matter. Lock your device. Enable biometric access where possible. Avoid saving sensitive credentials in plain text. These habits reduce the impact if your device is lost or compromised.
Public Networks and Hidden Dangers
Connecting to public WiFi may feel harmless. Many users check balances or log into exchanges while traveling. This creates an opportunity for attackers to intercept traffic or inject malicious content. Unsecured networks lack proper encryption and can be manipulated easily.
Even a simple login session can be exposed under the wrong conditions. Attackers may create fake hotspots that look legitimate. Once connected, your data can be monitored without obvious signs. Understanding the risks outlined in public WiFi risks helps reinforce why caution is needed.
Using trusted networks or secure connections reduces this exposure. Avoid logging into sensitive accounts on unknown networks. If access is necessary, consider additional safeguards such as encrypted connections.
Common User Mistakes That Lead to Loss
Security issues often come from repeated patterns. These behaviors are easy to overlook but have serious consequences. Recognizing them early can prevent costly mistakes.
- Reusing passwords across exchanges and apps
- Clicking links from unsolicited emails or messages
- Downloading apps from unofficial sources
- Ignoring security alerts or unusual login activity
- Storing sensitive data in unprotected formats
Each of these actions creates an entry point. Attackers rely on predictable behavior. Breaking these patterns disrupts their strategy and protects your assets.
Practical Security Setup for Everyday Users
Building a secure routine does not require advanced technical knowledge. It requires consistency. Simple habits applied daily create strong protection over time.
- Use unique passwords for every platform
- Enable additional verification for all accounts
- Review login history regularly
- Keep devices updated with the latest patches
- Back up important data securely
These steps are straightforward but effective. They reduce exposure across multiple attack vectors and make your setup harder to compromise.
Understanding Threat Types in a Simple Way
| Threat Type | How It Works | Impact |
|---|---|---|
| Phishing | Fake links or emails capture login details | Account takeover |
| Malicious Apps | Hidden code collects data or redirects traffic | Data theft |
| Network Attacks | Intercepted connections on unsafe networks | Session hijacking |
| Credential Reuse | Leaked passwords used across platforms | Multiple account breaches |
Staying Alert to Subtle Warning Signs
Not all attacks are obvious. Some happen quietly. A login alert from an unfamiliar location. A delayed withdrawal. A slight change in app behavior. These signals often go unnoticed. Paying attention to them allows early intervention.
Checking account activity regularly helps identify unusual patterns. Responding quickly can limit damage. Many platforms offer notification features. Enabling them provides an extra layer of awareness.
For broader understanding of safe online practices, guidance from staying secure online highlights how everyday habits influence digital safety across different environments.
Building Long Term Confidence With Safer Habits
Security is not a one time setup. It evolves as threats change. Staying informed and adjusting your habits keeps your defenses strong. Small improvements made consistently have a lasting effect.
Confidence in using exchanges and apps comes from control. Knowing how to verify platforms, protect accounts, and respond to risks makes a difference. It allows you to use Bitcoin tools without unnecessary exposure.
Every action counts. Logging in carefully. Checking links before clicking. Keeping devices clean and updated. These choices build a strong foundation. Over time, they reduce the chances of loss and improve overall security.
Protecting Bitcoin is not about complexity. It is about awareness and discipline. The more intentional your actions are, the safer your experience becomes.















No Responses